Introduction to Ledger Live Login
Ledger Live is the official application for managing cryptocurrencies using Ledger hardware wallets. To access your Ledger Live account, you must perform a secure login that ensures your private keys remain protected. Ledger Live login is the gateway to sending, receiving, staking, and monitoring your crypto assets. This guide provides a detailed overview of the login process, security practices, troubleshooting, and best practices for managing your portfolio safely.
As the cryptocurrency ecosystem grows in 2025, Ledger Live login has become more critical for users who wish to securely manage digital assets without exposing private keys to online threats.
What Is Ledger Live?
Ledger Live is a software platform designed to manage Ledger hardware wallets, including the Ledger Nano X, Nano S Plus, and Ledger Stax. It allows users to access their wallets, monitor balances, send and receive cryptocurrencies, stake supported coins, swap assets, and interact with Web3 services securely. Ledger Live does not store private keys on the computer; instead, all transactions require device confirmation, maintaining the security of your funds.
Ledger Live Login – Why It Matters
Ledger Live login is a secure entry point into your crypto portfolio. Unlike web wallets or exchange platforms, Ledger Live ensures that private keys remain on the device. Even if your computer is compromised, login alone cannot expose your funds. This makes Ledger Live login one of the safest ways to access and manage your cryptocurrencies.
Step-by-Step Ledger Live Login Guide
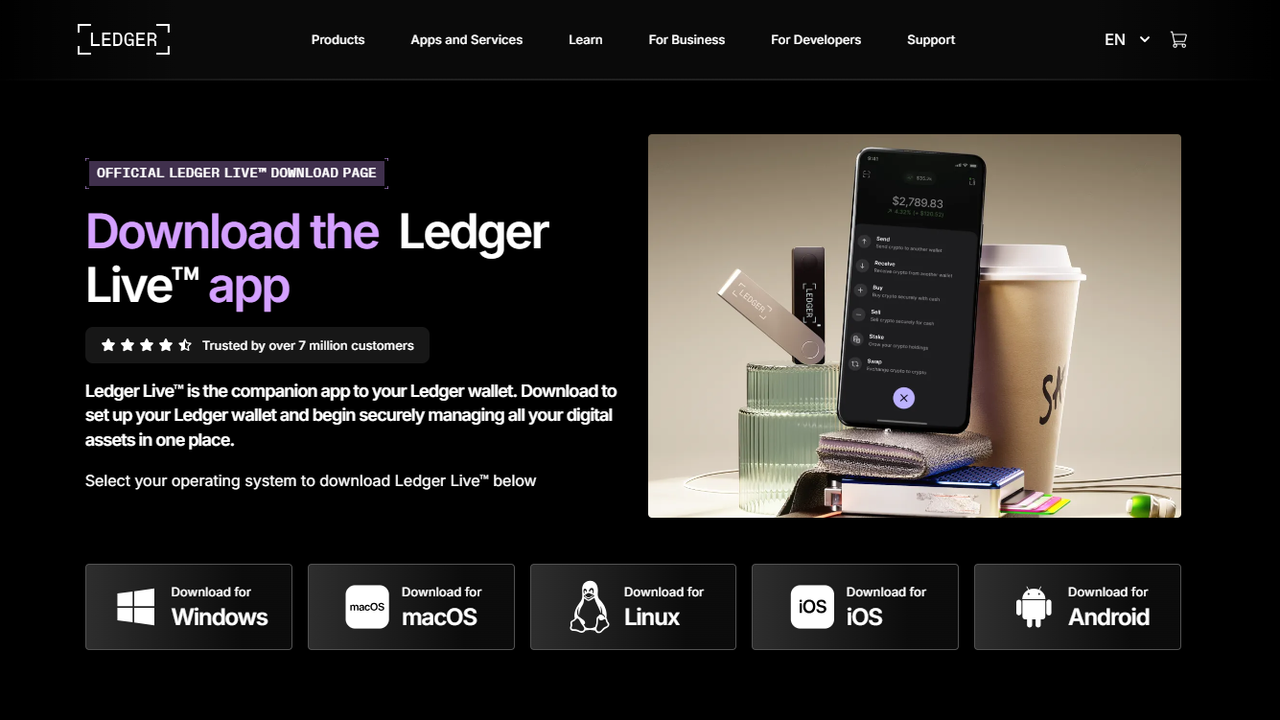
Step 1: Download and Install Ledger Live
Ledger Live is available for Windows, macOS, Linux, Android, and iOS. Always download the application from the official website (ledger.com) to avoid phishing attacks. After downloading, install the application by following on-screen instructions.
Step 2: Launch Ledger Live
Open Ledger Live on your device. If this is your first login, you will be prompted to set up a new device or recover an existing wallet.
Step 3: Connect Your Ledger Device
Use the official USB cable to connect your Ledger hardware wallet. Ledger Live will detect the device and provide prompts to proceed with login. Make sure your device is authentic and the seal is intact.
Step 4: Enter PIN Code
Enter the PIN code set on your Ledger device. This PIN protects your wallet from unauthorized access. If you enter the wrong PIN multiple times, the device will temporarily lock to prevent brute-force attacks.
Step 5: Confirm Device Authentication
Ledger Live requires device confirmation for login and subsequent actions. Verify the on-screen instructions and accept login only on your hardware device.
Recovering Access to Ledger Live
Using Recovery Phrase
If you lose access to your Ledger device, you can recover your Ledger Live account using the 24-word recovery phrase. Connect a new Ledger device, select "Restore Wallet," and carefully input your recovery phrase. This will restore your accounts, balances, and transaction history.
Forgot PIN
If you forget your PIN, you will need to reset the device and restore it using the recovery phrase. Ledger Live login will then resume normal access.
Managing Accounts After Login
Adding Cryptocurrency Accounts
Ledger Live supports multiple cryptocurrencies, including Bitcoin, Ethereum, USDT, ADA, DOT, and many ERC-20 tokens. After login, you can add accounts by selecting the respective cryptocurrency and following on-screen instructions.
Sending Crypto
- Choose the account and click "Send."
- Enter the recipient address and amount.
- Confirm the transaction on your Ledger device to ensure security.
Receiving Crypto
- Select the account and click "Receive."
- Verify the receiving address on your Ledger device.
- Share the verified address for secure deposits.
Swapping Crypto
Ledger Live integrates with trusted exchange partners, allowing users to swap one cryptocurrency for another safely. All swaps are confirmed via the Ledger device.
Staking Crypto
Ledger Live supports staking for multiple coins such as Ethereum, Tezos, Cardano, Polkadot, and Solana. Staking directly through Ledger Live ensures your private keys remain offline while earning rewards.
Ledger Live Security Features
- PIN and passphrase protection.
- Offline signing of transactions.
- Encrypted firmware updates to ensure authenticity.
- Verification of addresses on-device before sending funds.
- Anti-phishing alerts and secure app management.
Troubleshooting Ledger Live Login
Device Not Recognized
- Ensure you are using the original USB cable.
- Try a different USB port.
- Restart Ledger Live and reconnect the device.
- Update firmware and Ledger Live to the latest version.
PIN Issues
- If you forget your PIN, reset the device and restore using the recovery phrase.
- Ensure proper PIN entry to avoid temporary lockouts.
Recovery Phrase Issues
- Check the order and spelling of each word carefully.
- Use the device interface to input words correctly.
Best Practices for Secure Ledger Live Login
- Always download Ledger Live from the official website.
- Never share your PIN or recovery phrase.
- Verify all addresses on the hardware device before sending crypto.
- Keep Ledger firmware and Ledger Live updated.
- Use a passphrase for additional hidden wallets if needed.
Conclusion
Ledger Live login is the secure entry point for managing your Ledger hardware wallet. By following the official steps, setting strong PINs, and using the recovery phrase correctly, you can ensure your cryptocurrencies remain safe. Ledger Live provides a powerful, user-friendly interface for sending, receiving, staking, and swapping crypto while maintaining offline security.
In 2025, Ledger Live continues to be one of the most trusted platforms for secure cryptocurrency management, and following these login procedures ensures your digital assets are always protected.